Quantum Computing’s Impact on US Encryption Standards: 2026 Readiness Guide
US businesses must understand quantum computing’s impending impact on current encryption standards by January 2026 to proactively safeguard sensitive data and ensure compliance with evolving cybersecurity frameworks.
The digital landscape is constantly evolving, and with it, the threats that challenge our cybersecurity. One of the most significant shifts on the horizon is the advent of quantum computing, poised to revolutionize various sectors, but also presenting an unprecedented challenge to existing encryption methods. This article explores Quantum Computing’s Impact on US Encryption Standards: What Businesses Need to Know by January 2026 to Prepare for Future Threats. The time to act and understand these implications is now, as the deadline for proactive measures rapidly approaches.
Understanding the Quantum Threat to Current Encryption
Quantum computing, while still in its nascent stages, holds the potential to break many of the cryptographic algorithms that secure our digital communications and data today. Businesses in the US must grasp this fundamental threat to adequately prepare for a future where classical encryption may no longer be sufficient. The computational power of quantum machines could render current security protocols obsolete, creating vulnerabilities across all industries.
Traditional encryption relies on the mathematical difficulty of solving certain problems, like factoring large numbers or computing discrete logarithms. These problems are practically impossible for even the most powerful supercomputers to solve in a reasonable timeframe. However, quantum computers, using principles like superposition and entanglement, can tackle these problems with astonishing efficiency.
Shor’s Algorithm and Grover’s Algorithm
Two quantum algorithms, in particular, pose a direct threat to current encryption standards:
- Shor’s Algorithm: This algorithm can efficiently factor large numbers, directly compromising widely used public-key cryptography schemes such as RSA and elliptic curve cryptography (ECC). These are fundamental to securing web traffic (HTTPS), digital signatures, and many other online transactions.
- Grover’s Algorithm: While not breaking symmetric-key ciphers outright, Grover’s algorithm significantly reduces the effective key length, making brute-force attacks much more feasible. This means that algorithms like AES would need larger key sizes to maintain the same level of security against quantum adversaries.
The looming threat isn’t just theoretical; research and development in quantum computing are accelerating globally. Businesses cannot afford to wait until a fully fault-tolerant quantum computer is readily available. The window for preparation is narrowing, making the January 2026 timeline a critical benchmark for action.
In conclusion, the fundamental mechanisms of quantum computing directly challenge the mathematical foundations of our current encryption. Understanding algorithms like Shor’s and Grover’s is the first step for businesses to comprehend the scale of the impending cybersecurity paradigm shift and begin formulating their defense strategies.
The NIST Post-Quantum Cryptography Standardization Process
Recognizing the urgent need for new cryptographic standards, the National Institute of Standards and Technology (NIST) initiated a comprehensive process to identify and standardize post-quantum cryptographic (PQC) algorithms. This global effort is crucial for establishing the next generation of encryption that can withstand attacks from quantum computers. For US businesses, aligning with NIST’s recommendations is paramount for future security compliance.
NIST’s PQC standardization process began in 2016, inviting cryptographic researchers worldwide to submit candidate algorithms. This multi-round competition has involved rigorous evaluation, public scrutiny, and cryptanalysis to filter out weaker proposals and identify the most robust solutions. The goal is to select algorithms that are not only quantum-resistant but also efficient and practical for real-world deployment.
Key Milestones and Selected Algorithms
The standardization process has progressed through several rounds, with NIST recently announcing its initial set of chosen algorithms. These include:
- CRYSTALS-Kyber: Selected for general encryption, suitable for establishing secure keys in protocols like TLS. It offers strong security based on lattice problems.
- CRYSTALS-Dilithium: Chosen for digital signatures, vital for authenticating software, transactions, and documents. Like Kyber, it leverages lattice-based cryptography.
- FALCON and SPHINCS+: Also selected for digital signatures, offering alternative approaches and diversity in cryptographic primitives. FALCON is lattice-based, while SPHINCS+ is hash-based.
These selections mark a significant step, providing businesses with concrete algorithms to begin evaluating and integrating. However, the process is ongoing, with more algorithms expected to be standardized, particularly for additional digital signature schemes and key encapsulation mechanisms. Businesses should monitor NIST’s updates closely, as these selections will form the bedrock of future US encryption standards.
The NIST PQC standardization initiative provides a clear roadmap for developing quantum-resistant encryption. US businesses must actively follow this process, understanding the selected algorithms and their implications, to ensure their cryptographic infrastructure remains resilient against emerging quantum threats.
Why January 2026 is a Critical Deadline for US Businesses
The date January 2026 isn’t arbitrary; it represents a critical inflection point for US businesses, driven by a combination of technological advancements, government directives, and the inherent ‘harvest now, decrypt later’ threat. Understanding the urgency behind this deadline is essential for proactive planning and avoiding significant security risks in the near future.
The ‘harvest now, decrypt later’ scenario is a major concern. Malicious actors, including state-sponsored entities, are already collecting encrypted data today, anticipating that they will be able to decrypt it once powerful quantum computers become available. This means that sensitive information encrypted with current standards, even if secure today, could be compromised years down the line. For data with long-term confidentiality requirements, such as medical records, intellectual property, or government secrets, this poses an immediate threat.


Government Directives and Industry Pressure
US government agencies, particularly the National Security Agency (NSA) and the Cybersecurity and Infrastructure Security Agency (CISA), have issued directives and guidance emphasizing the need for a transition to PQC. These directives are not merely suggestions; they signal an imminent shift in regulatory and compliance requirements that will cascade down to businesses interacting with government entities or operating in critical infrastructure sectors.
Furthermore, industry leaders and cybersecurity experts are increasingly advocating for early adoption. Waiting until quantum computers are fully operational would be a catastrophic mistake, as the time required to inventory cryptographic assets, migrate systems, and re-certify applications is substantial. A delayed response could lead to widespread data breaches, financial losses, and reputational damage.
The January 2026 deadline serves as a stark reminder for US businesses to initiate their PQC transition strategies. It’s a call to action to mitigate the ‘harvest now, decrypt later’ risk and align with evolving government and industry expectations, ensuring long-term data security.
Assessing Your Current Cryptographic Footprint
Before any transition to post-quantum cryptography can begin, businesses must undertake a thorough assessment of their existing cryptographic footprint. This involves identifying every instance where encryption is used, understanding the algorithms currently deployed, and evaluating the sensitivity of the data being protected. This discovery phase is often the most challenging but is absolutely critical for a successful migration.
Many organizations have a complex and often undocumented cryptographic landscape. Encryption is embedded in various layers of IT infrastructure, from network protocols (VPNs, TLS/SSL) to application-level security, data at rest (disk encryption, database encryption), and digital signatures for code integrity. Without a clear inventory, identifying all vulnerable points becomes impossible.
Key Steps in Cryptographic Assessment
- Inventory all cryptographic assets: This includes hardware security modules (HSMs), cryptographic libraries, certificates, encryption keys, and the applications that rely on them. Documenting these assets provides a baseline for understanding the scope of the migration.
- Identify algorithms and protocols in use: Determine which specific algorithms (e.g., RSA, ECC, AES) and protocols (e.g., TLS 1.2, SSH, IPsec) are currently implemented. This helps pinpoint direct vulnerabilities to quantum attacks.
- Evaluate data sensitivity and lifespan: Classify data based on its confidentiality requirements and how long it needs to remain secure. Data that must remain confidential for decades is at higher risk from ‘harvest now, decrypt later’ attacks.
- Map dependencies: Understand which systems, applications, and services rely on specific cryptographic primitives. A change in one area could have ripple effects across the entire IT ecosystem.
This comprehensive assessment will reveal the scale of the migration challenge and allow businesses to prioritize their efforts. It also provides an opportunity to streamline cryptographic practices, update outdated systems, and improve overall security posture. Without this foundational understanding, any attempt at PQC migration will be haphazard and likely ineffective.
In essence, a detailed cryptographic assessment is the indispensable first step for US businesses. It provides the necessary visibility into existing vulnerabilities and dependencies, enabling a structured and prioritized approach to the upcoming post-quantum transition.
Developing a Robust Post-Quantum Migration Strategy
Once a business has a clear understanding of its cryptographic footprint, the next crucial step is to develop a comprehensive post-quantum migration strategy. This strategy should be multi-faceted, addressing not only the technical aspects of algorithm replacement but also organizational, budgetary, and operational considerations. A well-planned strategy ensures a smooth transition with minimal disruption.
The migration to PQC will not be a single, instantaneous event but rather a phased process. It requires careful planning, resource allocation, and a deep understanding of the interdependencies within an organization’s IT infrastructure. Early engagement with vendors and technology providers is also vital, as many will be developing PQC-compliant solutions.
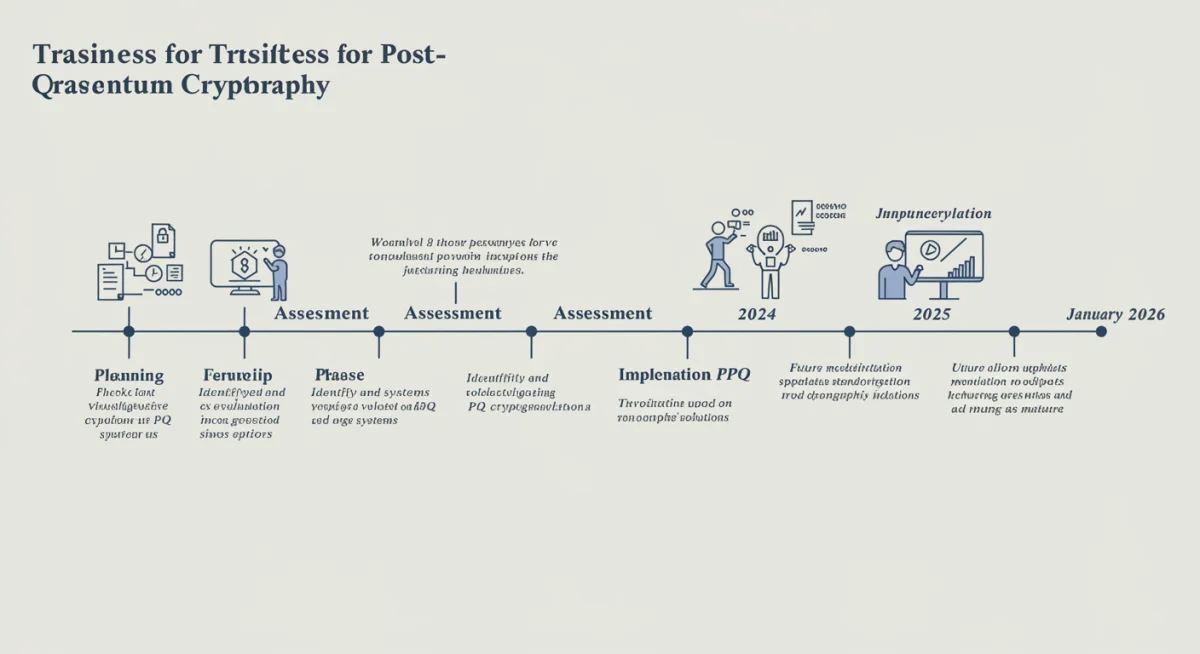

Key Components of a PQC Migration Plan
- Pilot Programs and Testing: Begin with small-scale pilot programs to test selected PQC algorithms in non-critical environments. This allows for performance evaluation, compatibility checks, and identification of potential issues before widespread deployment.
- Agile and Hybrid Approaches: Consider using hybrid cryptography, where both classical and post-quantum algorithms are used in parallel. This provides a layered defense, offering protection against both classical and quantum attacks during the transition period. An agile approach allows for flexibility as NIST standards evolve.
- Vendor Engagement: Work closely with software and hardware vendors to understand their PQC roadmaps. Prioritize solutions that offer cryptographic agility, allowing for easy swapping of algorithms as new standards emerge or threats evolve.
- Talent Development and Training: Invest in training cybersecurity teams on PQC concepts, selected algorithms, and migration best practices. The skills required for PQC implementation and management will be critical.
- Budget and Resource Allocation: Secure adequate budget and resources for the migration. This includes costs for new hardware, software upgrades, training, and potential consulting services.
A robust PQC migration strategy must also include a clear communication plan to inform stakeholders about the changes, their implications, and the benefits of the transition. This proactive approach fosters understanding and minimizes resistance. The goal is to build a crypto-agile infrastructure that can adapt to future cryptographic shifts beyond just quantum threats.
In conclusion, developing a robust PQC migration strategy involves a systematic, phased approach that integrates technical implementation with organizational readiness. By focusing on pilot programs, hybrid solutions, vendor collaboration, and talent development, US businesses can effectively navigate the transition to quantum-resistant encryption.
Compliance, Governance, and Future-Proofing Your Business
Beyond the technical implementation of post-quantum cryptography, US businesses must also consider the broader implications for compliance, governance, and long-term future-proofing. The shift to PQC is not merely an IT project; it’s a strategic imperative that influences risk management, regulatory adherence, and competitive advantage. Proactive engagement in these areas will define an organization’s resilience in the quantum era.
Regulatory bodies, both domestic and international, are beginning to incorporate PQC readiness into their compliance frameworks. For industries subject to stringent data protection regulations, such as healthcare (HIPAA), finance (PCI DSS), and government contractors (DFARS), demonstrating a clear plan for PQC migration will become a non-negotiable requirement. Non-compliance could lead to severe penalties, legal liabilities, and loss of trust.
Establishing Strong Governance and Policy
- Updated Cryptographic Policies: Review and revise existing cryptographic policies to explicitly include PQC requirements, guidelines for algorithm selection, key management, and deprecation of vulnerable systems.
- Risk Management Frameworks: Integrate quantum risk into enterprise-wide risk management frameworks. Assess the potential impact of quantum attacks on critical business operations and data assets.
- Supply Chain Security: Evaluate the quantum readiness of your supply chain partners. A chain is only as strong as its weakest link, and third-party vulnerabilities could compromise your PQC efforts.
- Regular Audits and Reviews: Implement regular audits to ensure PQC compliance and the ongoing effectiveness of implemented solutions. The cryptographic landscape will continue to evolve, requiring continuous monitoring and adaptation.
Future-proofing your business means building an infrastructure that is cryptographically agile. This design principle allows for the rapid swapping of cryptographic algorithms without extensive system overhauls, ensuring that your organization can adapt to future threats, whether from quantum advancements or other unforeseen cryptographic breakthroughs. Investing in crypto-agility today will save significant costs and effort in the long run.
Ultimately, the transition to post-quantum cryptography is a journey towards enhanced security and regulatory compliance. By focusing on robust governance, updated policies, and strategic future-proofing through crypto-agility, US businesses can ensure their long-term viability and protect their most valuable assets against the quantum threat.
Best Practices for a Smooth PQC Transition by 2026
Achieving a smooth and effective transition to post-quantum cryptography by January 2026 requires more than just technical knowledge; it demands strategic planning, organizational alignment, and adherence to established best practices. Businesses that approach this challenge systematically will be better positioned to safeguard their data and maintain operational continuity in the quantum era.
One of the foremost best practices is to start early. The complexity of identifying all cryptographic dependencies, testing new algorithms, and rolling out changes across diverse systems means that procrastination is not an option. The ‘big-bang’ approach to PQC migration is fraught with risk; a phased, iterative strategy is far more prudent.
Recommended Actions for Businesses
- Form a Dedicated PQC Task Force: Assemble a cross-functional team including IT, security, legal, and business unit representatives to oversee the entire migration process. This ensures all aspects of the business are considered.
- Prioritize Critical Systems and Data: Begin the transition with the most sensitive data and business-critical systems that have long-term security requirements. This mitigates the highest risks first.
- Adopt Crypto-Agility Principles: Design new systems and update existing ones with cryptographic agility in mind. This means making it easy to swap out cryptographic algorithms as standards evolve without requiring major architectural changes.
- Stay Informed on NIST Progress: Continuously monitor NIST’s PQC standardization updates and guidance. Their recommendations will be the authoritative source for compliant algorithms and deployment strategies.
- Engage with Cybersecurity Experts: Consider consulting with PQC specialists or cybersecurity firms that have expertise in quantum-safe cryptography to guide your migration efforts.
- Educate Stakeholders: Ensure that executive leadership and relevant employees understand the importance and implications of the PQC transition to secure necessary resources and support.
Testing is another critical best practice. Thoroughly test new PQC implementations in non-production environments to identify performance bottlenecks, compatibility issues, and any unforeseen vulnerabilities. This iterative testing approach minimizes disruption when algorithms are deployed to production systems. Moreover, remember that PQC is not a one-time fix but an ongoing commitment to cryptographic hygiene.
In summary, a smooth PQC transition by 2026 hinges on proactive planning, strategic prioritization, and continuous engagement with evolving standards. By adopting these best practices, US businesses can effectively prepare for the quantum threat and ensure the enduring security of their digital assets.
| Key Aspect | Brief Description |
|---|---|
| Quantum Threat | Quantum computers can break current encryption (RSA, ECC), enabling ‘harvest now, decrypt later’ attacks. |
| NIST Standardization | NIST is standardizing post-quantum algorithms (e.g., Kyber, Dilithium) for future security. |
| January 2026 Deadline | Critical for proactive PQC migration to counter data harvesting and meet future compliance. |
| Migration Strategy | Assess current crypto, develop phased plans, engage vendors, and adopt crypto-agility. |
Frequently Asked Questions About Quantum Encryption
Post-quantum cryptography refers to cryptographic algorithms designed to be secure against attacks by both classical and quantum computers. These new algorithms are being developed to replace current standards that are vulnerable to quantum threats.
January 2026 is a crucial milestone for businesses to begin their transition to PQC. It addresses the ‘harvest now, decrypt later’ threat, where encrypted data collected today could be compromised by quantum computers in the future. It also aligns with anticipated government mandates.
NIST has initially selected CRYSTALS-Kyber for general encryption and CRYSTALS-Dilithium, FALCON, and SPHINCS+ for digital signatures. Businesses should prioritize evaluating and planning for these, while also monitoring NIST’s ongoing standardization process for further selections.
Crypto-agility is the ability of a system to quickly and easily switch between different cryptographic algorithms or parameters. It’s crucial for PQC migration because it allows businesses to adapt to evolving standards and new threats without significant system redesigns.
Small businesses should start by inventorying their critical data and encryption use. They should engage with their IT providers, prioritize PQC-ready solutions, and stay informed on NIST guidance. Even small steps taken now can make a big difference.
Conclusion
The impending impact of quantum computing on US encryption standards presents both a significant challenge and an opportunity for businesses to bolster their cybersecurity posture. The January 2026 deadline is not a distant threat but a critical call to action, urging organizations to move beyond awareness and into comprehensive planning and implementation of post-quantum cryptography. By understanding the quantum threat, following NIST’s standardization process, meticulously assessing current cryptographic assets, and developing robust migration strategies, businesses can ensure their data remains secure against future adversaries. Proactive engagement with PQC principles, alongside strong governance and a commitment to crypto-agility, will not only meet emerging compliance requirements but also future-proof operations in an increasingly complex digital world. The journey to quantum-safe security is underway, and preparedness today is the key to resilience tomorrow.





